DoD 5220.22-M Data Wipe Method
DoD 5220.22-M is a software based data sanitization method used in various file shredder and data destruction programs to overwrite existing information on a hard drive or other storage device. Erasing a hard drive using the
DoD 5220.22-M data sanitization method will prevent all software based file recovery methods from lifting information from the drive and should also prevent most if not all hardware based recovery methods. The DoD 5220.22-M method is often
incorrectly referenced as DoD 5220.2-M (.2-M instead of .22-M).
![]() DoD 5220.22-M Wipe Method
DoD 5220.22-M Wipe Method
The DoD 5220.22-M data sanitization method is usually implemented in the following way:
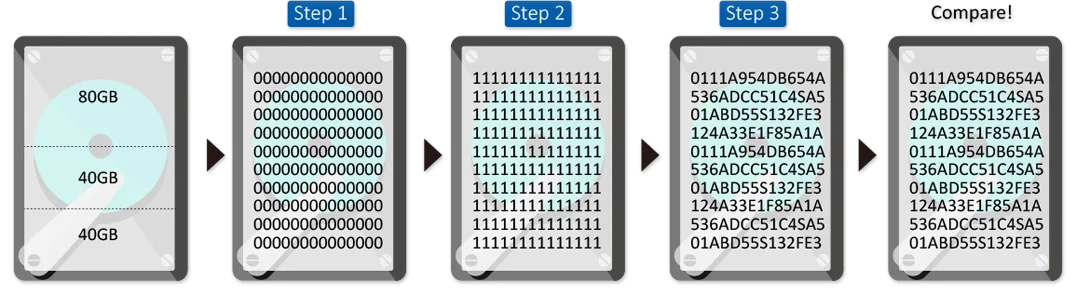
Pass 1: Writes a zero and verifies the write
Pass 2: Writes a one and verifies the write
Pass 3: Writes a random character and verifies the write
You might also come across various iterations of DoD 5220.22-M including DoD 5220.22-M (E), DoD 5220.22-M (ECE), or others. Each will probably use a character and its compliment (as in 1 and 0) and varying frequencies of verifications. While less
common, there's another altered version of DoD 5220.22-M that writes a 97 during the last pass instead of a random character.
![]() More About DoD 5220.22-M
More About DoD 5220.22-M
The DoD 5220.22-M sanitization method was originally defined by the US National Industrial Security Program (NISP) in the National Industrial Security Program Operating Manual (NISPOM), located below, and is one of the most common
sanitization methods used in data destruction software. Most data destruction programs support multiple data sanitization methods in addition to DoD 5220.22-M, like Secure Erase
, RCMP TSSIT OPS-II, CSEC ITSG-06, Write Zero, Random Data and Schneier.
Note: The NISPOM does not define any US government standard for data sanitization. The Cognizant Security Authority (CSA) is responsible for data sanitization standards.
The DoD 5220.22-M method is no longer permitted (nor is any software based data sanitization method) for use by various members of the CSA including the Department of Defense, the Department of Energy, the Nuclear Regulatory
Commission, and the Central Intelligence Agency.
![]() Is DoD 5220.22-M Better Than Other Methods?
Is DoD 5220.22-M Better Than Other Methods?
It probably doesn't matter all that much which data wipe method you use. Since most of us who are wiping our hard drives are only doing so before we sell the drive or install a new OS, it shouldn't be such a huge concern as to how many random
characters are being written to the drive versus ones or zeros. Plus, most people who try to recover data from a purchased hard drive are probably using everyday tools like Recuva, and while they work for uncovering deleted data, they don't do
well when a data wipe method was performed.
However, when choosing a data sanitization method, you might consider how long it will take to wipe the drive. If you have a really large hard drive, Write Zero will take much less time to finish than DoD 5220.22-M, which will be much quicker than
one like Gutmann which might run through over 30 passes. Also consider whether verifications are done after the passes. Since some software might implement the DoD 5220.22-M method in a way that verifies each write at the end of each pass, the
whole process will take longer than using a different wipe method that doesn't verify at all (like Secure Erase) or waits until the very end of the last pass to verify that the data has
been overwritten. Another factor that might determine which method you use is the actual data that's used to overwrite the hard drive. Some wipe methods, like Write Zero, just use a zero instead of random characters. It's possible that using random
characters makes it less likely that the data can be recovered.
-
 NISPOM DoD 5220.22-M
NISPOM DoD 5220.22-M
Language: EN - File: 2,0 MB
Copyright ©2001-2025 Virtual Vision, all rights reserved.
All prices and specifications are subject to change and availability.
All offers and orders are subject to our general terms and conditions. Please take note of our disclaimer and
privacy policy. Type errors as well as price changes reserved.

